Single sign-on
How to enable Single Sign-On for your team
Single sign-on (SSO) is a feature that allows you to give your team members one login for all of the platforms your company uses. If you’re an Enterprise client with access to SSO, you can require your team to log in to Lexer using their SSO credentials. This article will walk you through what it is, how it works, and its setup.
How it works
SSO means that your team members will not log in with their Lexer password, but will instead be directed to your company identity provider to authenticate. This ensures that only active employees from your team can access your Lexer account. It also allows you to enforce your own password policy, multi-factor enrolment rules, and IP whitelisting.
Your team will continue to access Lexer from clients.lexer.io/login; however, when they provide their email address and click ‘Next’, we will check to see if SSO is required for their account and will route them to your company’s identity provider for authentication. Once they have successfully authenticated with their employee credentials, they are sent back to Lexer with permission to access the platform.
We can enforce SSO for your team in two ways:
- Anyone in your team with a company email address must authenticate with SSO.
- Anyone in a particular group in your team must authenticate with SSO.
Once a user is authenticated using your company identity provider, their Lexer Groups will control access to products, integrations, and feature permissions.
Setup
Configuring SSO for your team requires no setup in your account, and is completely managed by Lexer and your IT administrator. We will configure all of the technical information on your behalf, removing the headache of finding URLs and Certificates.
Your IT administrator will create a Lexer SSO config and provide us with the following:
- Entity ID - the Identity Provider Entity ID, also called Issuer URL.
- SSO URL - the URL used to login to your identity provider.
- Certificate - X.509 certificate offered by your identity provider.
Lexer will configure your SSO and provide your IT administrator with:
- Assertion Consumer Service URL.
- Audience URI.
Lexer will assist your IT team in verifying the connection to ensure your team can authenticate using your identity provider. Finally we will enable SSO required for your team and their next login will require authentication via your identity provider.
Additional technical information:
- Lexer supports SAML 2.0.
- NameID field is to contain the user’s email address. No other attributes are required.
- SAML2 request binding is HTTP Post.
- Request signature algorithm is SHA-256.
User provisioning
Adding new team members to your Lexer account will require an invite from someone in your team with manager permissions. New users will receive a welcome email, instructions to create their account, and will require SSO authentication on their first login. New users will still set up a password in case SSO is ever disabled for your Lexer account.
Access is revoked as soon as a team member is disable in your company identity provider. Their account will continue to exist in Lexer until they are archived or deleted.
What it looks like
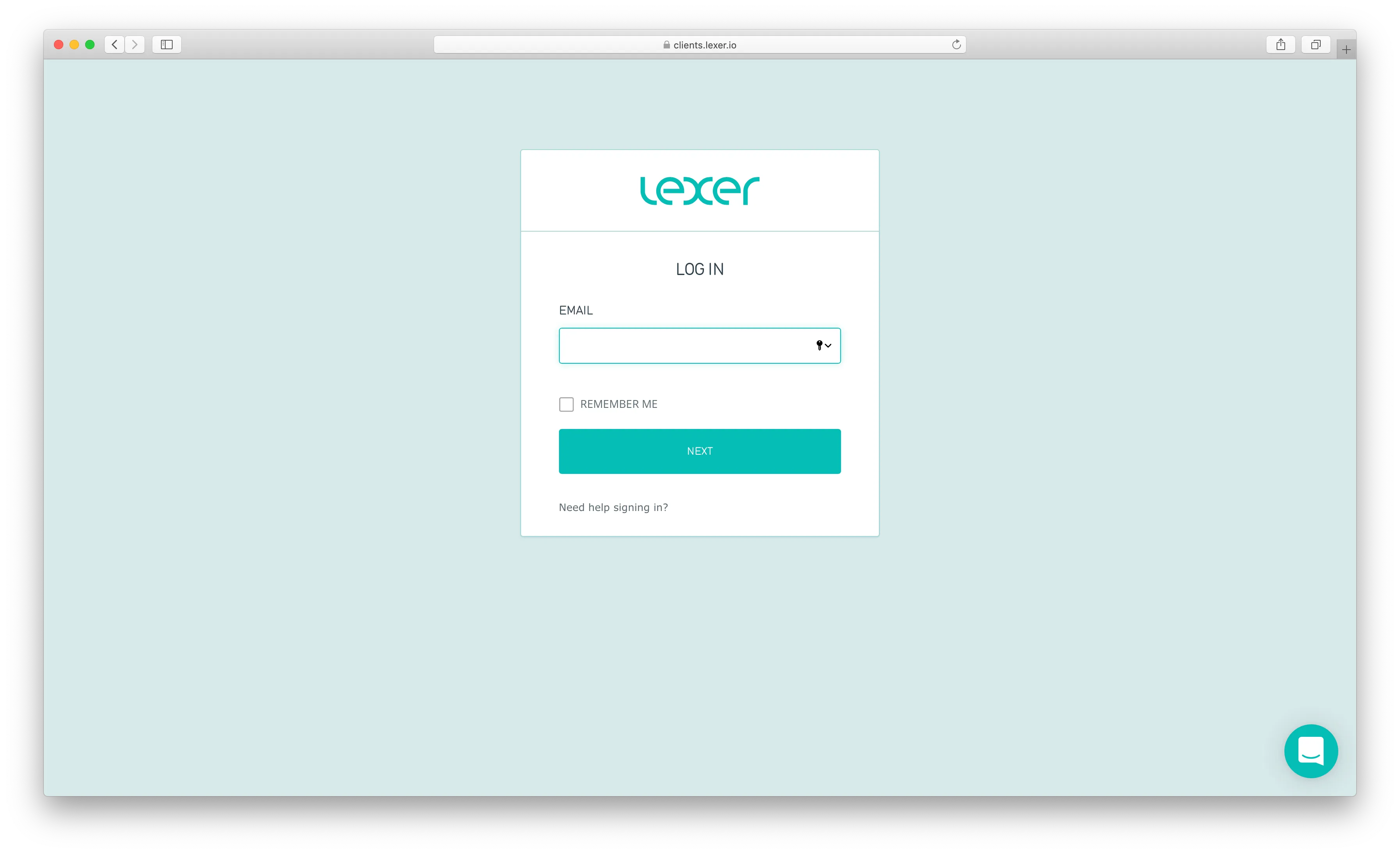
Your team will continue to log in at clients.lexer.io by providing their email address:
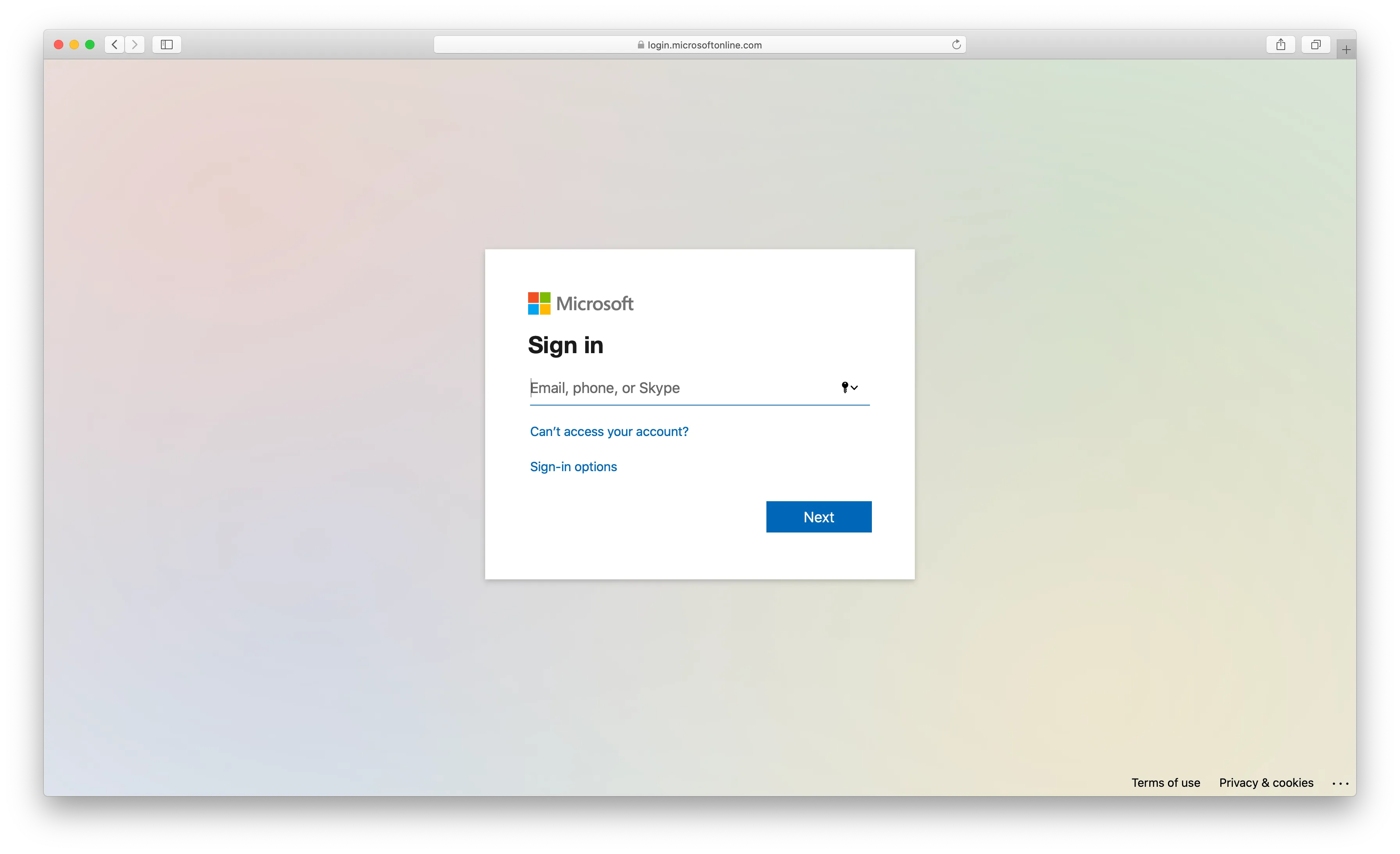
Then our routing rule will detect that SSO is enabled for that user, and will direct them to your company authentication page. For example, if you're using Microsoft Azure, it will look like this:
Once you have successfully authenticated your team will be taken to the Lexer home page.
Let’s get started
That's all for Single sign-ons and now you can get in touch with your Lexer Success Manager who can help you setup SSO for your team.

